Introduction
Spoofing modules enable Man-in-the-Middle (MITM) attacks on local networks.
What is a MITM Attack?
Section titled “What is a MITM Attack?”A man-in-the-middle attack (MITM) intercepts communication between two parties. The attacker secretly relays and can alter messages. Both parties believe they are communicating directly with each other.
How It Works
Section titled “How It Works”The attack follows a simple pattern:
- Position: The attacker places themselves between victim and destination
- Intercept: All traffic flows through the attacker’s machine
- Relay: Messages are forwarded, optionally modified
Network MITM Example
Section titled “Network MITM Example”When you connect to a network, the router forwards your packets to their destination.
In a MITM attack, we spoof the router’s address. The network then considers our device as the router.
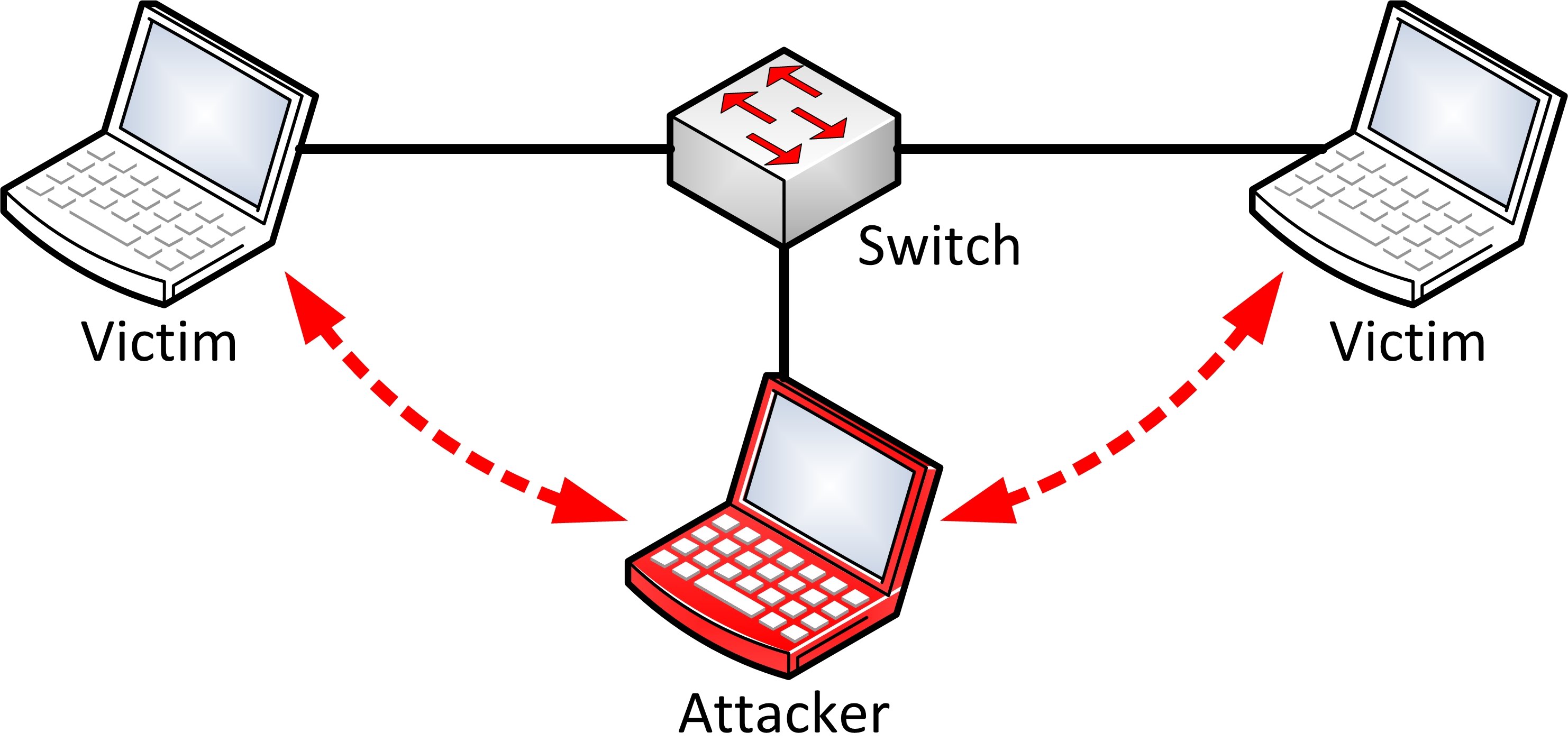
Once positioned, all network traffic flows through your computer. This enables:
- Sniffing: Capture emails, passwords, cookies
- Proxying: Intercept and modify HTTP/HTTPS requests
- Injection: Replace content, kill connections, redirect traffic
Available Spoofing Modules
Section titled “Available Spoofing Modules”| Module | Protocol | Description |
|---|---|---|
| arp.spoof | ARP/IPv4 | Spoof ARP replies to intercept IPv4 traffic |
| ndp.spoof | NDP/IPv6 | Spoof neighbor advertisements for IPv6 networks |
| dns.spoof | DNS | Reply to DNS queries with spoofed responses |
| dhcp6.spoof | DHCPv6 | Attack Windows hosts via DHCPv6 responses |